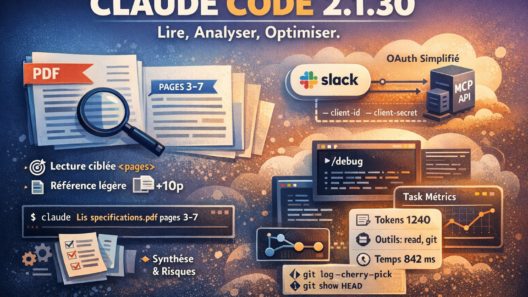
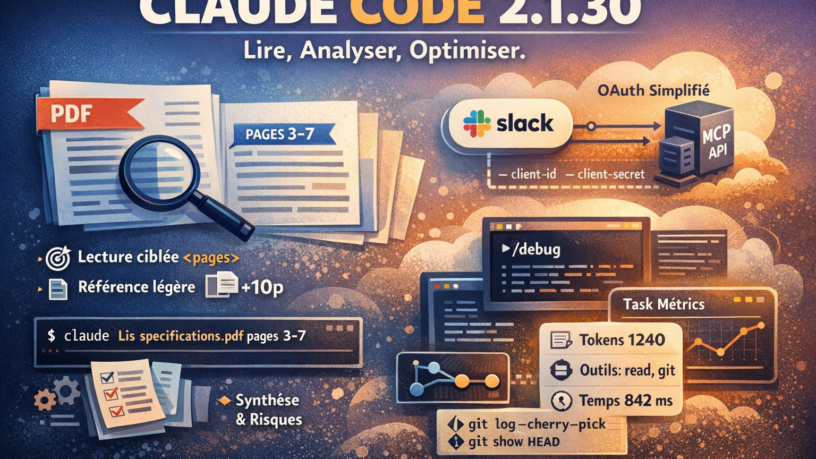
Update : Claude 2.1.30 and PDF saves the tokens
Some releases make a lot of noise. Others focus on refining what already exists, removing friction, and making tools more reliable day after day.Claude Code 2.1.30 clearly belongs to the…
Update PHP 8.5.2
Corrections targeting the core of the language and several standard extensions.They aim to improve the consistency of internal behaviors, error handling, and memory safety, without modifying…
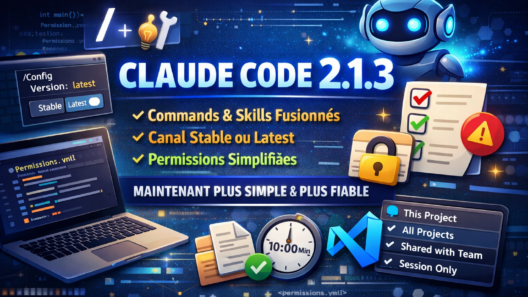
UPDATE : Claude Code 2.1.3
Anthropic has just released version 2.1.3 of Claude Code, its development assistant available from the command line and in VS Code.This update doesn’t revolutionize the tool, but it fixes…
Understanding Neural Networks and Artificial Intelligence
Neural networks are at the heart of modern artificial intelligence. They allow machines to learn from data, and they’re everywhere: voice assistants, machine translation, image recognition,…
A nice phishing attempt
A few weeks ago I suffered a rather impressive phishing attempt via Twitter. I wanted to analyze it, understand why it didn’t work, and how the attacker could have done it…
WSL2 : Command Survival Guide
This article is a CheatSheet dedicated to WSL2 (Windows subsystem for Linux), a kind of memo, or survival guide in the list of useful commands.I tried to write down all the commands that are…
My IPhone is tracking my activities
IPhone, Apple, Google, Facebook, Whatsapp, IOS, Android, Internet… Trackers, control and security of your data… Find out how your devices intelligently track your activity on the internet.
User Favourites
Nothing found!
You Might Like
Nothing found!
Short Reads
Nothing found!